What's New
You can now use API Keys to authenticate the users behind the applications making API calls to Clarizen One. Access Keys make it easier to manage those users and their applications, which include custom integrations and cloud-based services, such as SCIM-based user provisioning.
Benefits
Using API Keys instead of username and password credentials provides the following advantages:
- Improved user authentication and management, so less maintenance and effort for admins:
- More visibility and control for admins with dedicated system settings
- API keys have later expiration dates (1 year)
- Secondary key for easy refreshing and continuous service
- Enhanced security - User credentials are not saved locally
How it Works
1. In Clarizen One
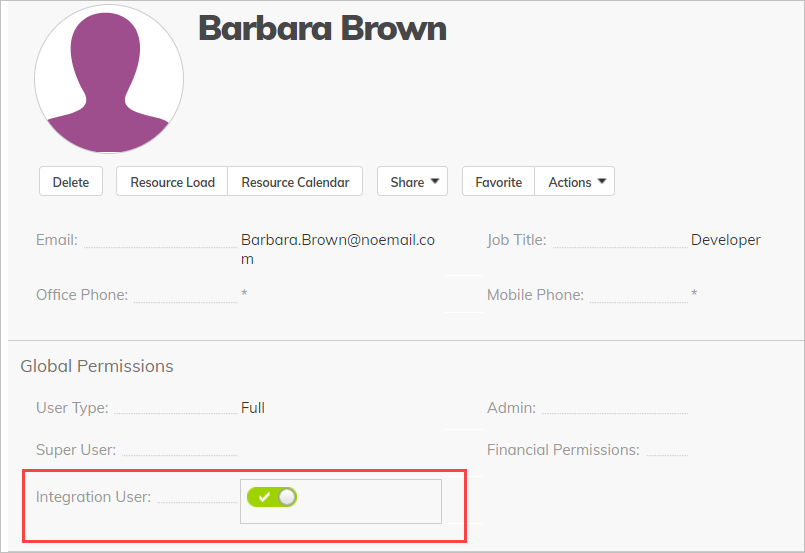
- In the user's settings under Global Settings, enable Integration User.
Note about the Integration user
We recommend creating a unique Integration-type user for each 3rd-party integration. The Integration user should not be the Admin user, but should have at least Lite Admin permissions. - Generate the API Key(s). The Integration User can now go to Personal Settings > Integration Settings and click Manage API Keys.
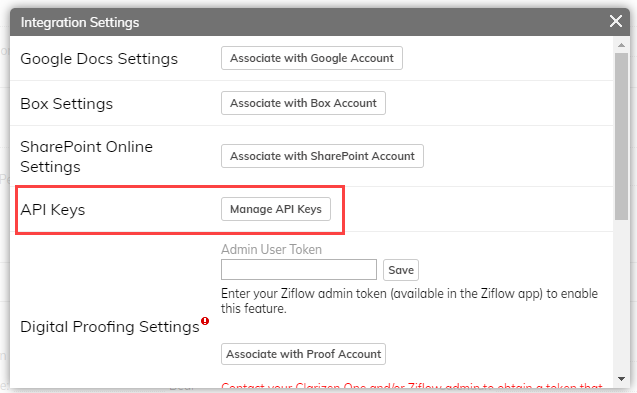
- You can now generate the primary and secondary keys. After you click Generate, the key is copied to your clipboard, and you can paste the key in the 3rd-party app.
Note: Once the dialog is closed, the key cannot be copied or pasted.
Here you can also see when a key is going to expire or when a key expired.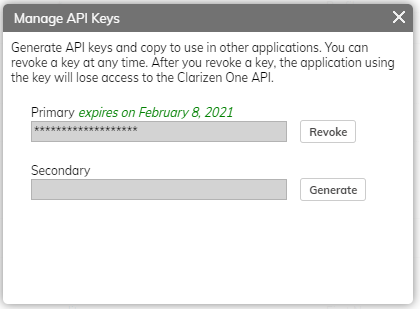
Terminating API Access
You can terminate access to the API by:
- For integration users
- Revoking a key in the Integration Settings described above.
- For admins
- Disabling the Integration User role under the user's Global Settings, described above. This will also delete any Access Keys used by that user.
- Suspending or deleting the Integration user. This will also delete any API Keys used by that user.
2. In the 3rd-Party Integrate App
You can use API keys by:
- Using a dedicated interface to store the API keys in your 3rd-party app or by modifying the authorization header of API calls
- In all cases, for an API Key to work properly, a 3rd-party application must pass a new “ApiKey” (case insensitive) attribute in the authorization header with the actual generated JWT key appended to it:
ApiKey [key]
Comments